The Ultimate Showdown Cripsa vs Others
Date Created: 22 Apr 2023Share:

Comparison with Other Service Providers (like WorkOs, Stytch etc.)
Cripsa Backend architecture mostly uses AWS Serverless Technologies. The general advantages of using the serverless technology is as follows:
- Cost Savings: With serverless computing, you only pay for the actual usage of your application or service, rather than for the infrastructure required to run it. This means you can save money on hardware, software, and maintenance costs.
- Scalability: Serverless computing can automatically scale up or down to handle varying levels of demand, so you can avoid over-provisioning and paying for resources you dont need. This can improve application performance and reduce costs.
- Reduced Operational Overhead: Serverless computing eliminates the need for you to manage and maintain servers, which can be time-consuming and resource intensive. AWS takes care of all the underlying infrastructure, so you can focus on writing code and delivering value to your customers.
- Increased Agility: With serverless computing, you can quickly develop and deploy applications and services without worrying about infrastructure requirements. This can reduce time-to-market and enable you to respond more quickly to changing business needs.
- Improved Reliability: AWS serverless technology provides built-in fault tolerance and automatic recovery, which can improve the availability and reliability of your applications and services.
- Greater Security: AWS serverless technology provides a secure infrastructure with built-in security features, including encryption, identity and access management, and network security. This can help you protect your data and applications from potential security threats.
Cripsa Technology is running on AWS and leveraging serverless technology, hence our clients can benefit from the advantages of serverless computing as well. Our clients can enjoy cost savings, scalability, reduced operational overhead, increased agility, improved reliability, and greater security, all because of the underlying infrastructure provided by AWS. This can give our clients a competitive advantage, as they can focus on delivering value to their own customers without worrying about the underlying infrastructure requirements.
One such example of Improved reliability can be visualized by seeing the Availability SLA metrics on different services of AWS, which Cripsa Technology is using in its product.
The SLA for different services used by Crips product is as follows:
API Gateway |
99.95% * |
Lambda |
99.95% * |
S3 |
99.9% * |
Cognito |
99.9% * |
Secrets Manager |
99.9% * |
Route 53 (For Frontend portal) |
100.0% * |
ELB/ALB/NLB (For Frontend portal) |
99.99% * |
EC2 (For Frontend portal) |
99.99% * |
EBS (For Frontend portal) |
99.99% * |
EFS (For Frontend portal) |
99.9% * |
ECS (For Frontend portal) |
99.99% * |
Above data shows that our product provides, almost 100% (approx.) availability and thus our client will enjoy uninterrupted services.
- Cripsa is entirely running on AWS Cloud Premium service. All the Backend service where User details are maintained are managed services by AWS. Thus, accidental loss of data is unlikely. Also, since it is AWS managed services so availability or data loss due to human error is negligible, which is an added advantage against our competitors.
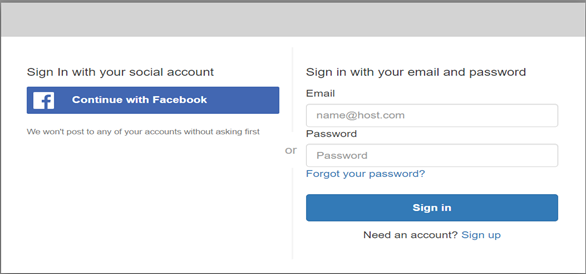
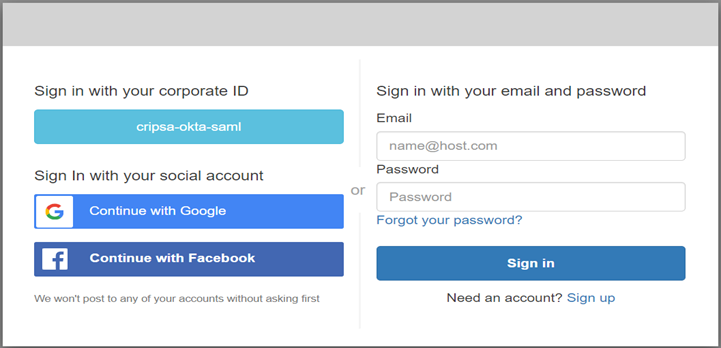
- Cripsa has provided various options through which our customer can have various Authentication features like SAML/OIDC, OAuth2.0 and Password-MFA all will be on the same login prompt. They have the flexibility to choose either one or two or all of the Authentication feature. The following figure will give more clarity on this feature:
Cripsa Technology is GDPR Compliant:
GDPR stands for General Data Protection Regulation, which is a regulation in the European Union that was enacted to protect the privacy and personal data of EU citizens. It imposes strict rules and requirements on how organizations collect, store, process, and share personal data.
Cripsa Technology utilizing AWS Cognito, a service offered by Amazon Web Services, that provides authentication, authorization, and user management for web and mobile applications. Cognito is designed to help organizations handle user data in a way that is compliant with GDPR.
To comply with GDPR, AWS Cognito provides several features, including:
- User Consent: Cognito enables you to obtain user consent before collecting and storing their personal data. You can configure Cognito to require consent for specific data fields and provide users with the ability to view and manage their data.
- Data Portability: Cognito enables users to export their data and take it with them if they choose to switch to a different service. This ensures that users have control over their data and can exercise their right to data portability under GDPR.
- Data Deletion: Cognito provides a mechanism to delete user data upon request. This enables users to exercise their right to be forgotten under GDPR.
- Data Encryption: Cognito encrypts all user data at rest and in transit, which helps to protect the confidentiality and integrity of personal data.
In summary, Cripsa Technology is designed to help organizations comply with GDPR by providing features that enable user consent, data portability, data deletion, and data encryption.
Also, if there is a requirement of maintaining user profile in the country of origin of the user, then Cripsa will develop a setup through which user data of specific country will be stored in the Database which runs on the Datacenter of that country where user/client belongs to.
- Cripsa Technology has been designed and configured in such a way that the end user can get seamless high-performance response. The below diagram gives a glimpse on how Cripsa has maintained high security landscape together with low latency between different service communications.
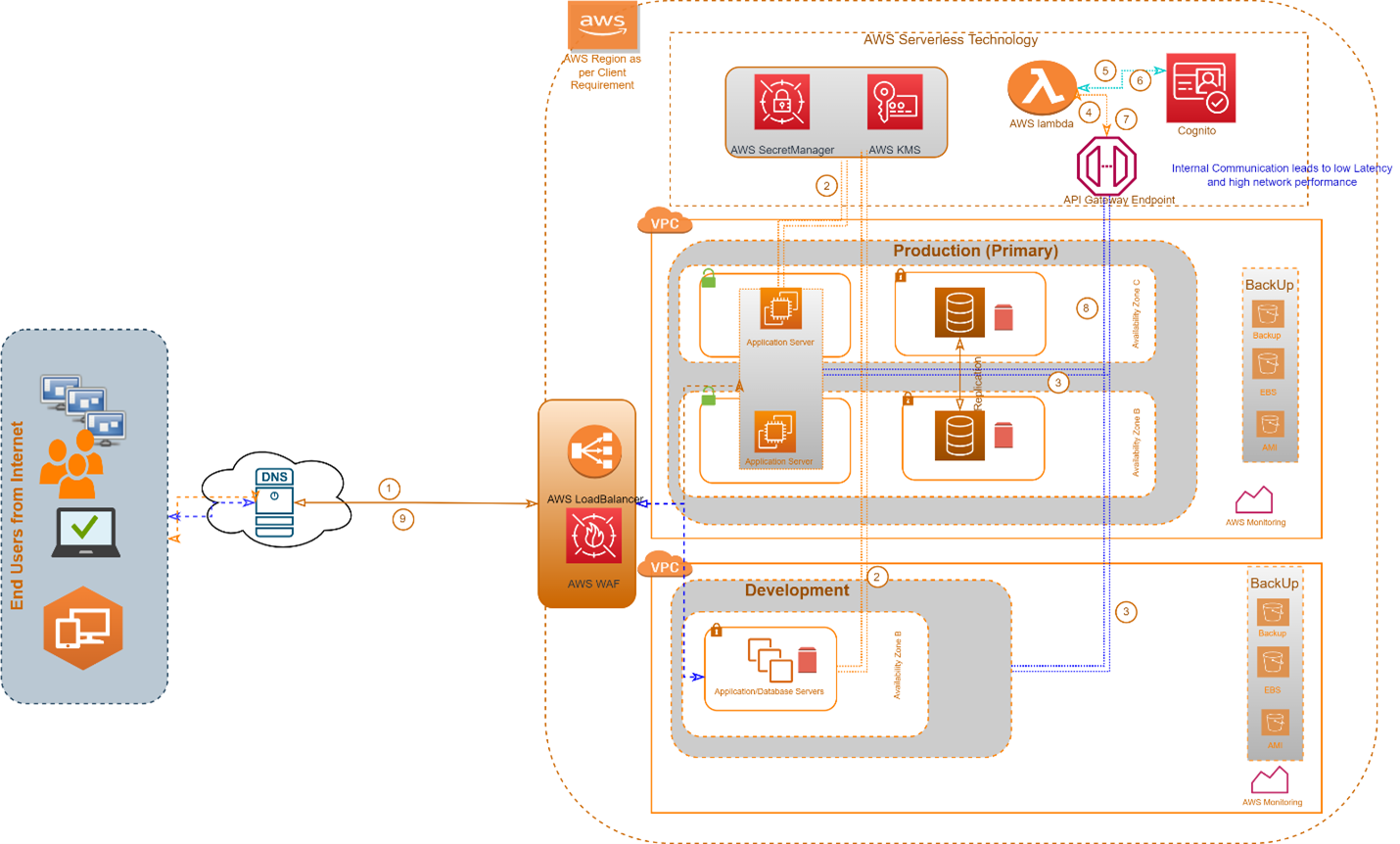
By utilizing AWS WAF (Web Application Firewall) and AWS Load Balancer, Cripsa can secure its own landscape and prevent issues like DDoS attacks. When Cripsas customers utilize the product, they dont have to worry about such Denial-of-Service attacks due to unauthorized internet users because the AWS WAF can help protect against common web exploits and attacks, including DDoS attacks.
In addition to that, by using API Keys and authorization given to its clients for the rotation of the key, Cripsa can further secure the landscape. API Keys provide a secure way to authenticate and authorize access to APIs, which can help protect against unauthorized access and misuse of data. By rotating the keys regularly, Cripsa can further enhance the security of its APIs and reduce the risk of unauthorized access.
Overall, by utilizing AWS WAF, Load Balancer, and API Keys, Cripsa can provide a more secure and reliable product to our customers, helping to prevent security incidents and ensuring the privacy and integrity of our customer data.

